Critical Infrastructure
through Technology & Innovation.
and manufacture of Power Distribution
Solutions for global Data Centres.
Critical Infrastructure
through Technology & Innovation.
design and manufacture
of Power Distribution Solutions
for Global Data Centres.
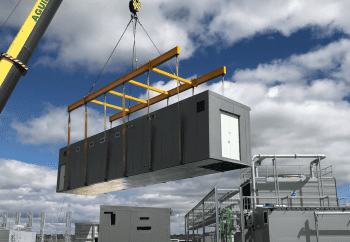
TES Power
TES are world leading specialists in the design, manufacture and installation of critical power distribution and monitoring systems for Data Centre projects worldwide.
TES Water
TES specialise in the provision of municipal water and wastewater treatment facilities. We provide mechanical, electrical, instrumentation, control, automation (MEICA), minor civil works and process solutions to our clients.